Рама и Каросерия Тегличи Opel Astra, 2001г., ID:u145236 - Обява Продава Части за Автомобили и Джипове

Купете ТЕГЛИЧ OPEL Astra K Sports Tourer (B16) (11.2015 - 2023) на ниски цени » висококачествени резервни части за Теглич / монтажни компоненти
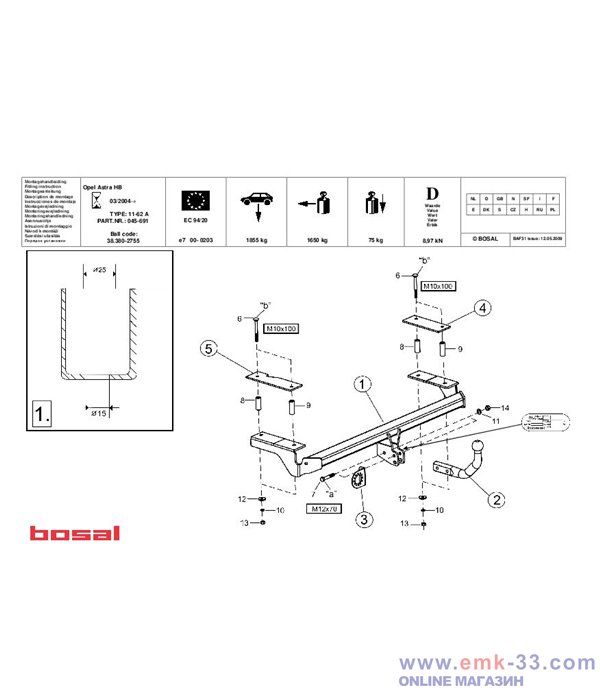
![Теглич за OPEL ASTRA H 08.04-05.14 със стационарна присъединителната кука с болтове [9847] - TPS Garage Теглич за OPEL ASTRA H 08.04-05.14 със стационарна присъединителната кука с болтове [9847] - TPS Garage](https://tpsgarage.com/product_images/bdf02f4c2cdd07547acfe4e0229db917.jpg)