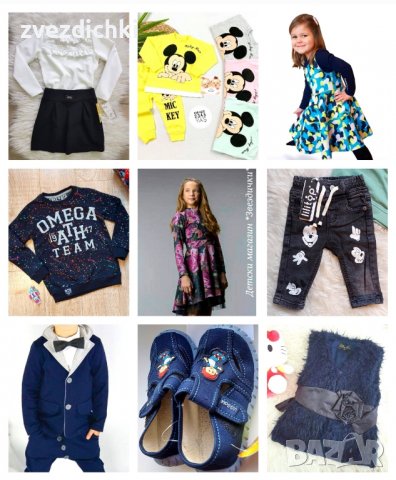
Търговия на едро маркови детски дрехи пакет - OVS деца микс - Испания, Нови - платформа за търговия на едро | Merkandi B2B

Наличност на нови маркови детски дрехи - Онлайн търговец на едро - Испания, Нови - платформа за търговия на едро | Merkandi B2B

Наличност на нови маркови детски дрехи - Онлайн търговец на едро - Испания, Нови - платформа за търговия на едро | Merkandi B2B

Наличност на нови маркови детски дрехи - Онлайн търговец на едро - Испания, Нови - платформа за търговия на едро | Merkandi B2B

Търговия на едро маркови детски дрехи пакет - OVS деца микс - Испания, Нови - платформа за търговия на едро | Merkandi B2B



%20(1)-262x343.jpg)